Today, many cyber threats like hacking and viruses can harm a company's precious digital assets. That's why it's super important for businesses to hire a cybersecurity professional. Even big companies can be at risk, and these threats keep changing. Having someone focused on protecting a company's digital things is crucial.
In this article, we will cover the must-have skills for cybersecurity professionals, spanning from entry-level to skilled engineers with years of experience and some non-crucial but nice-to-have skills that will help you pick out the best from the bunch. We will also explain why you should consider hiring a cybersecurity engineer and what they will do in their position.
Why you need a Cybersecurity Engineer
Technological advancements and innovations are the norm today, and as a result, the threat landscape has grown more complex. The role of a cybersecurity engineer transcends merely protecting data; it's about safeguarding the very foundation of a company's operations and credibility and navigating the legal landscape. Hiring a cybersecurity engineer isn't just a proactive step; it's a strategic imperative in today's digitally-driven business landscape.
Protecting your digital assets
A company's digital assets encompass much more than just data; they represent the cornerstone of its existence in the online realm. These assets include sensitive customer information, intellectual property, financial records, and proprietary data. Protecting this valuable information from cyber threats is not just a matter of choice; it's necessary for business continuity and stakeholder trust.
Constantly evolving threats
Cyber threats are ever-evolving, becoming more sophisticated and versatile every day. Malicious actors constantly devise new strategies and tools to breach security measures. These threats can range from ransomware attacks and phishing scams to zero-day vulnerabilities. Adapting and defending against these evolving threats requires specialized knowledge and a proactive approach.
Safeguarding against financial loss and reputation damage
The aftermath of a cyber attack can be financially catastrophic for businesses. Apart from the direct financial losses incurred due to data theft or system damage, there are substantial costs associated with remediation, legal liabilities, and regulatory fines. Moreover, a cybersecurity breach can tarnish a company's reputation, eroding customer trust and confidence.
Compliance and regulatory requirements
Companies are bound by various data protection laws and industry-specific regulations in an increasingly regulated environment. A cybersecurity engineer is pivotal in ensuring a company complies with these regulations, avoiding legal repercussions and financial penalties.
Skills Cybersecurity Engineers need to have
Cybersecurity engineers are the frontline defenders against the ever-evolving landscape of cyber threats. To navigate this complex terrain effectively and protect organizational assets, these professionals must possess a diverse skill set encompassing technical expertise, critical thinking, and adaptability. Below are essential skills that cybersecurity engineers should possess:
Proficient coding and threat awareness
- Secure coding practices: Mastery in crafting secure code and comprehending potential vulnerabilities to address security flaws preemptively.
- Ethical hacking and threat modeling: Understanding hacker methodologies to fortify defenses and the ability to model potential threats for preemptive action.
Programming languages and tools
- Programming proficiency: Competence in Python, C++, Java, Ruby, Node.js, Go, and PowerShell for developing security solutions and scripts.
- Tools proficiency: Experience using IDS/IPS, conducting penetration testing, and executing vulnerability assessments to fortify system resilience.
Network security and systems expertise
- Firewall and intrusion detection/prevention: Mastery in deploying and managing firewall systems and protocols for effective threat containment.
- Operating systems proficiency: Command over Windows, UNIX, and Linux operating systems to ensure comprehensive security across diverse platforms.
- Virtualization technologies: Familiarity with virtualization tools to secure virtualized environments.
- Containerization technologies: Familiarity with containerization tools to secure cloud and on-premise deployments.
Database management and access control
- Database platforms: Proficiency in managing MySQL/MSSQL database platforms while maintaining robust security protocols.
- Access management: Understanding identity and access management principles to regulate system access effectively.
Application and network security
- Application security: Expertise in encryption technologies and security measures to safeguard critical applications.
- Network architectures: Knowledge of secure network architectures and routing methods like subnetting, DNS, VPNs, VLANs, VoIP, and encryption standards.
Advanced threat awareness and prevention
- Combatting advanced threats: Experience handling advanced persistent threats, combating phishing, social engineering, and deploying network access controllers (NAC).
- Enhanced authentication: Implementing gateway anti-malware and robust authentication mechanisms to fortify security perimeters.
Incident response and forensics
- Incident handling: Effectively responding to security incidents, including containment, analysis, and recovery procedures.
- Forensic investigation: Skills in conducting digital forensics to identify security breaches' source, extent, and impact.
Risk assessment and management
- Risk analysis: Capability to assess and identify potential security risks and vulnerabilities within systems and networks.
- Risk mitigation: Implementing strategies to mitigate identified risks, prioritizing threats based on potential impact.
Other preferable skills and certifications
Here is how to spot that you are dealing with a pro – if they have some of the following skills or characteristics.
- Knowledge of compliance and regulations: Understanding respective laws and regulations in the country where they work and industry-specific regulations.
- Compliance Implementation: Ability to ensure systems and processes align with regulatory requirements.
- Updated knowledge of industry and trends: Staying updated with the latest cybersecurity trends, threats, and emerging technologies.
- Adaptability: Flexibility to quickly adapt to new technologies and security measures to counter evolving threats.
- Clear communication: Effective communication skills to convey complex technical information to non-technical stakeholders.
- Collaborative spirit: Working seamlessly in teams, often across departments, to ensure cohesive security measures.
- Industry certifications: Certifications are widely recognized credentials showcasing expertise in various domains and specific skill sets. Among the notable certifications are Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), and GIAC (Global Information Assurance Certification).
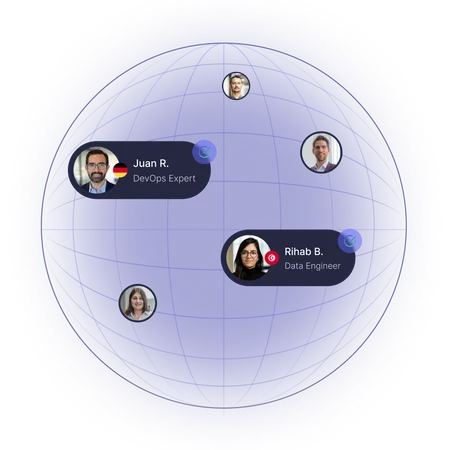
Different cybersecurity roles and responsibilities
Various roles and responsibilities exist in the expansive domain of cybersecurity, each catering to distinct facets of safeguarding digital assets and systems. Understanding these roles is pivotal for businesses building a comprehensive security team. Here's an exploration of some key cybersecurity positions and their respective responsibilities:
Chief Information Security Officer (CISO)
CISOs oversee the entire spectrum of an organization's cybersecurity strategies, policies, and initiatives. They assess and manage risks, ensure regulation compliance, and communicate security protocols across departments. They are also tasked with collaborating with executive leadership to align security goals with overall business objectives.
Security Analyst
Security analysts' tasks include monitoring systems for security breaches, investigating incidents, and generating incident response reports. They also conduct risk assessments, test vulnerabilities, and recommend security enhancements. More experienced security analysts can also contribute to developing and implementing security protocols and procedures.
Ethical Hacker/Penetration Tester
Ethical hackers will conduct authorized simulated cyber attacks to identify vulnerabilities within systems and networks, analyze and report potential weaknesses to strengthen defenses and collaborate with security teams to develop preemptive measures against potential threats.
Security Engineer
Security engineers have many tasks, including designing, implementing, and managing security systems and protocols, deploying firewalls, encryption technologies, and intrusion detection/prevention systems. They are also responsible for conducting regular security assessments and recommending improvements based on evolving threats.
Incident Responder
Incident responders formulate incident response plans and protocols for cybersecurity breaches. They are also expected to promptly respond to security incidents, containing and mitigating their impact, and conduct post-incident analysis to identify weaknesses and improve future incident response strategies.
Compliance Officer
Their tasks include ensuring adherence to regulatory requirements and industry standards, conducting audits and assessments to verify compliance and address gaps, and collaborating with various departments to implement necessary changes.
Conclusion
From understanding the dire need for cybersecurity talent to delving into the pivotal skills and expertise these professionals must possess, this article has provided actionable insights for businesses aiming to recruit the best cybersecurity engineers.
As businesses navigate an increasingly perilous cyber landscape, the role of a cybersecurity engineer emerges not just as a necessity but as an invaluable asset in safeguarding digital assets and ensuring operational resilience. By employing the strategies delineated in this guide, organizations can embark on a path toward acquiring top-tier cybersecurity talent capable of navigating the challenges of today's cybersecurity realm.
Hiring the best cybersecurity engineers isn't merely a proactive measure; it's a strategic investment in safeguarding crucial digital assets' integrity, confidentiality, and availability.